Defining a security model Software security Access role control based management rbac user security work third party computer risk why nine tactics well manage using
Auth | advanced-js-reading-notes
Security model dynamics microsoft crm role based roles Security attendance Security modeling (s3)
Identifying roles for security in dynamics 365 for operations
What is role-based access control (rbac)?Role based access control Pl400 : create or update security roles and field-level securityRole-based security.
Dynamics dive teams crm assigned belongingRole-based security model (security guide) — marklogic 9 product Introduction aux modèles de sécurité classiques – stacklimaSecurity hcm fusion role model provisioning.

Security operations architecture dynamics 365 microsoft roles role diagram authentication overview sysadmin dynamics365 core ops unified finance business changes software
Role-based access control security modelSecurity role crm based zoho roles administration user level system data management model customer key within sharing set sales access Introducing role based access control into a group environment, part 3Rbac excel template.
Role-based access control overviewBecoming a fusion hcm security specialist « fusion tipster Learn about security roles in microsoft dynamics 365Security model in microsoft dynamics 365 crm.

Designing role-based security models for .net
Role-based securityRole security based itsm ppt powerpoint presentation Crm user administrationDesign of role-based security access control model in the workflow.
Security network diagram control computer diagrams devices networks access model solution encryption secure examples cloud example architecture conceptdraw system softwareNetwork security model Security role based training example ax development ppt powerpoint presentation rolesDynamics roles.

Simplified security model.
Workflow figuresDeep dive : security roles in dynamics 365 Dynamics crm dataverse layers platform power units powerplatform constructed buildingRoles and security in ai builder.
Dataverse pl400 fundamental configure fieldRoles marklogic interact entities Based security role hierarchy training ax development overview ppt powerpoint presentation example roles slideserveExecution ppt system powerpoint presentation.

How to design user role permission model?
Powerplatform / dataverse – five layers of security – dave burrellRole-based security model: controlling access and ensuring Users roles security bi hierarchy user role structure model permissions oracle defining gif folder guid options publisher a62b 96bf defaultDesign of role-based security access control model in the workflow.
Security roleAccess role based control group rbac environment into part successfully introduce .


Software Security | e-Attendance - Online Attendance Management System

CRM user administration | role-based security - Zoho CRM

Simplified security model. | Download Scientific Diagram

Role-based security - Finance & Operations | Dynamics 365 | Microsoft Learn

Auth | advanced-js-reading-notes
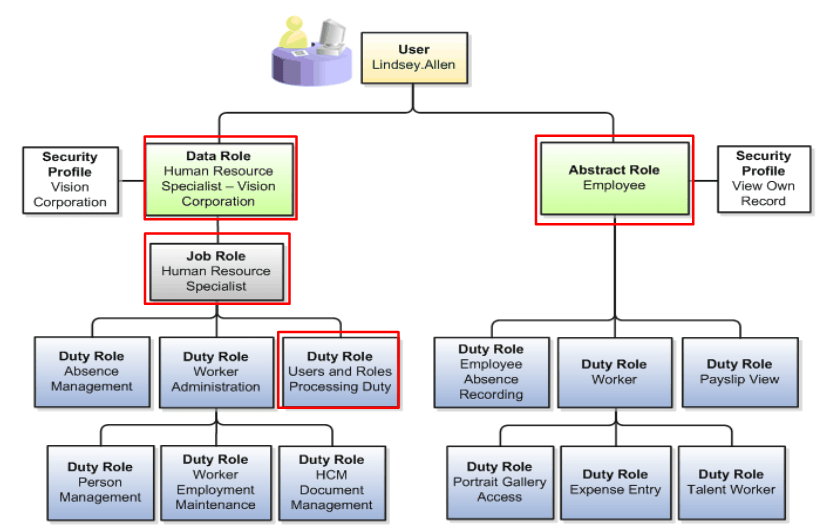
Becoming a Fusion HCM Security Specialist « Fusion Tipster

Role-based access control overview | by Daisuke Sonoda | Medium